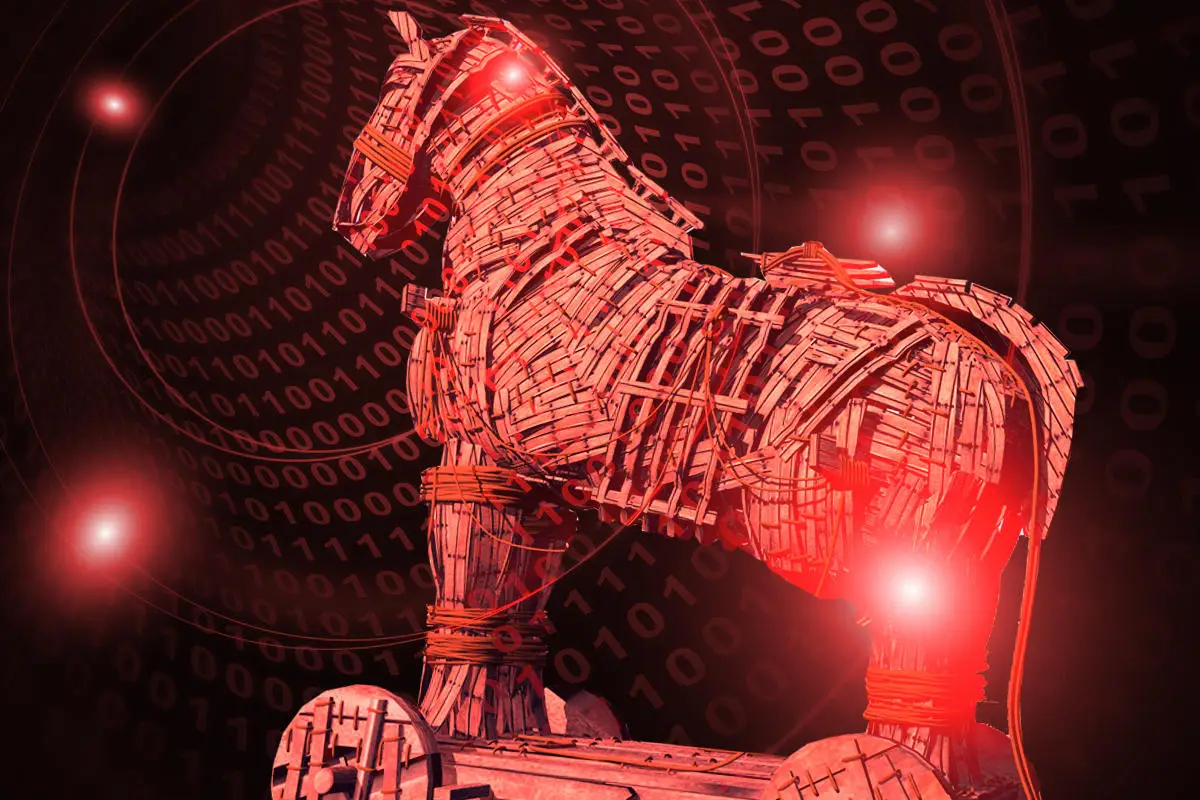
1. What is a Trojan horse?

A Trojan horse is a malicious program (malware) that intrudes under the guise of a seemingly harmless program and carries out various attacks. For example, although it looks like a simple document file or a useful application when you download it, it is infected with a malicious program inside.
Trojan horse
- email attachment
- Free apps distributed on the website
And so on, it exists in a form that makes you want to download it.
Once infected, the computer can be hijacked and used to attack other computers or steal data.
*The name Trojan comes from the Greek mythology of the Trojan Horse. When the Greeks went to war against the well-defended Troy, they would hide the Greek soldiers inside the giant wooden horse and trick the unsuspecting Trojans into carrying the horse into the Trojan castle. After that, Greek soldiers entered the castle with a wooden horses, opened the gates of Troy, and Troy fell.
Malware Trojan horses disguise themselves as safe programs to let users off guard and infiltrate computers and systems, secretly set up backdoors to invite new viruses, and steal important information. This behavior is very similar to the Trojan horse from Greek mythology, hence the name.
Here, we will explain the characteristics and types of this troublesome Trojan horse because it is difficult to notice that it has been infected.
1-1. Trojan horses are a type of malware
A Trojan horse is not strictly a virus, but a type of malware.
Malware is a name that combines “malicious” and “software” and is a general term for “malicious software. “
Once infected, the computer can be hijacked and used to attack other computers or steal data.
There are various types of malware, in addition to Trojan horses, viruses, spyware, ransomware, and malicious adware are types of malware.
| An example of malware and its characteristics | |
|---|---|
| trojan horse | Disguise itself as a harmless program and download it to your system or device to infect it |
| virus | Once infected, it spreads to multiple data files and devices like a virus. |
| spyware | Secretly send the user’s keyboard input contents, access history, etc. to the developer via the Internet |
| ransomware | Encrypts infected files to make them unusable and demands a ransom to unlock them |
| malicious adware | It is downloaded along with free apps, etc., and displays malicious advertisements such as products that can solve the problem along with false messages such as slow operation. |
1-2. Differences between Trojan horses and viruses
Trojan horses are technically malware, not viruses. Compared to viruses, they have the following characteristics :
| trojan horse | virus | |
|---|---|---|
| self-propagation | do not do | do |
| parasite | unnecessary | requirement |
| behavior | Act discreetly under the guise of a good program | Damage during activities that do not disguise is easy to see |
As mentioned above, Trojan horses have characteristics that make them suitable for continuing their malicious activities without being noticed. Viruses, on the other hand, are malware whose main purpose is to cause large-scale infection and damage in a short period.
Trojan horses are often thought of as viruses, but in reality, they are in completely different directions. By understanding the difference between the two, you will be able to take effective countermeasures, so let’s remember.
1-3. Major types of Trojan horses

There are several types of Trojan horses, depending on the method of attack. Typical examples include backdoors, keyloggers, password stealers, and proxies.
| Main types of Trojans | |
|---|---|
| back door |
|
| keylogger |
|
| password theft |
|
| proxy |
|
Malware “Emotet”, which has been increasing rapidly since February 2022, is also a Trojan horse. “Emotet” has a function to send an email with the title “Re:” added to the title of the previously sent and received email stored in the infected device. Recipients of “Emotet” emails will open the emails without any doubt that they are from someone they know, leading to a large-scale spread of infection.
2. Examples of damage caused by Trojan horse infection
The main damage caused by a Trojan horse infection is the leakage of personal information, which is used as a stepping stone for fraudulent activities, unauthorized use of credit cards, and unauthorized withdrawal of funds.
2-1. Leakage of personal information
Trojan infections often lead to the leakage of sensitive information, including personal information. Trojan horses can easily steal information through attack methods such as backdoors, keyloggers, and password theft.
Here, let’s check how information is leaked when infected with a backdoor Trojan horse.
[Specific example of personal information being leaked through a backdoor]
(1) Downloading attachment data (actually a Trojan horse) in an email sent from a business partner, and invading the company’s computer.
(2) A Trojan horse creates a backdoor on its own in the background
(3) A Trojan horse attacker remotely controls an infected computer via a backdoor to illegally view stored data, stealing and leaking personal information of customers and employees.
If customer information is leaked, the damage will spread not only to the company infected with the Trojan horse but also to the customer, making the situation even more serious.
In 2019, there was a case in which an employee’s computer at a public university was infected with a Trojan horse and the information of more than 18,000 emails was leaked. In this case, the infection route was through e-mail, but the source of the e-mail was an actual magazine company, so when I was careless and accessed the link, I was infected.
It is an example that makes us realize the importance of each individual’s countermeasures in that even an email that does not appear to be suspicious at first glance can be infected if you open the link easily.
2-2. Being used as a springboard for cheating
If you are infiltrated by a Trojan horse, it may be used as a stepping stone for cyber attacks such as DDoS attacks. This is very annoying because it puts the victim of the Trojan horse in the position of the perpetrator of the cyberattack.
[Specific example of being made a perpetrator of a DDoS attack]
(1) Downloading the data (actually a Trojan horse) of the website you always browse, and the Trojan horse infiltrates your company’s computer.
(2) A Trojan horse sends a large number of invalid packets to a specific site.
(3) On the site side, a large amount of work such as packet discard processing occurs, and if it becomes impossible to handle it, the server goes down.
In addition to DDoS attacks,
- Randomly distribute Trojan horses to business partners by e-mail
- Spread computer viruses indiscriminately, causing information leaks and system failures over a wide area
Such as, it may be used as a base for large-scale cyber attacks.
2-3. Unauthorized Use of Credit Cards and Unauthorized Withdrawal of Deposits
Fraudulent use of credit cards and fraudulent withdrawal of Internet banking deposits are common damages caused by Trojan horses. These are keylogger-type and password-theft-type attacks, and in addition to stealing IDs and passwords, there are also attack methods that lead to phishing sites.
[Specific example of being guided to a phishing site]
(1) By exploiting a vulnerability, a Trojan horse infiltrates a company device by accessing a site that has been fraudulently modified to infect a Trojan horse just by browsing the website.
(2) The Trojan waits until the compromised device accesses the targeted Internet banking site.
(3) At the moment when the intruded device accesses the target Internet banking site, a phishing site disguised as that site is set up and the user is prompted to enter their ID and password.
(4) Attackers fraudulently withdraw funds using IDs and passwords entered on phishing sites
According to the National Police Agency’s report on threats surrounding cyberspace in 2021, the number of phishing reports in 2021 was 526,504, the highest number in the past five years. It is necessary to be aware that damage caused by phishing sites is a familiar crime that anyone may encounter.
3. Four common Trojan infection routes and examples of countermeasures

The following are the four common Trojan horse infection routes and examples of countermeasures.
Understand the specific route of infection and take action to reduce the risk of infection.
3-1. Email and SMS
Email and SMS are the most common sources of Trojan infections.
In particular,
- Downloaded email attachments
- Clicking on the URL contained in the body of the email
- Accessed a link sent by SMS
You may be infected with a Trojan horse. Recently, there have been an increasing number of cases of people receiving SMS messages resembling absence notices from home delivery services, and accessing the links to become infected.
[Points to prevent infection]
- Don’t download attachments if you don’t know the content or need to download
- Do not blindly access URLs that do not need to be browsed
- Do not access unknown or unknown SMS links
3-2.SNS
In some cases, users are infected with Trojan horses by clicking URLs displayed in SNS messages.
This is because there are many cases where accounts are hijacked on SNS, and attackers sometimes pretend to be the account owner and paste URLs that infect Trojan horses.
[Points to prevent infection]
- Be careful when clicking URLs, even if they are messages from users you follow, and avoid accessing unknown URLs.
3-3. Website
Be careful when browsing websites. When you say “infected with a Trojan horse”, you may think of downloading something or clicking on a link, but there are cases where you are infected just by opening a website.
This is because a vulnerability in a website can be used to fraudulently deface the site so that a Trojan horse can be downloaded just by browsing.
[Points to prevent infection]
- On devices such as personal computers used for work, do not view sites other than those that are essential for work
- Install security software and avoid accessing sites that are deemed unreliable
3-4. File sharing
When sharing files in cloud storage, there are cases where an attacker saves a Trojan horse file in the shared folder and infects it by opening it.
Such infections can happen if you have set your file share permissions too broadly, or if an account with access privileges has been hijacked.
[Points to prevent infection]
- Pay attention to the setting range of access rights and properly manage IDs and passwords
- Enforce security measures for devices that can access cloud storage
4. Companies must take measures against Trojan horses!
Sharing Trojan protection and countermeasures is necessary for all companies for the following reasons:
| Why companies need Trojan protection |
|---|
|
4-1. Because infection routes are diverse and prevention is difficult without knowledge of countermeasures
Trojan horses spread through various channels such as e-mail, SNS, websites, etc. If you do not take proper measures, you will be infected immediately.
In companies, the risk of infection will be even greater as many employees read emails and use websites in their daily work. A single person accessing a link infected with a Trojan can compromise all computers and systems in the company.
Share with your employees how to prevent Trojan horse infection and what to do when infected, and use security tools to prepare for emergencies.
4-2. In the unlikely event that it is infected, your computer or system will be hijacked, leading to serious damage.
In the unlikely event that a company is infected with a Trojan horse, the damage is likely to be large, so it is necessary to take thorough measures.
This is because companies handle a large amount of important information such as personal information of customers, information of business partners, and confidential information. If a Trojan horse were to infect a company’s computer, there would be a risk that all of this would be leaked. There is also the risk that internal systems may be destroyed or hijacked and used as a means of attacking related parties.
To prevent irreversible damage, it is essential to take thorough measures.
5. What to do if you are infected with a Trojan horse
There are three things you should do first if you are infected or suspected to be infected with a Trojan horse.
| What to do first if infected with a Trojan horse |
|---|
|
1. Disconnect from the network 2. Remove with security software 3. Contacting parties with whom data is exchanged, such as business partners |
After taking these actions to prevent the further spread of the infection, it would be a good idea to conduct a detailed investigation of the infected device, take additional measures, and make necessary reports.
5-1. Disconnect from network
The first thing to do is disconnect any suspected infected device from the network. Disconnect and isolate all connections, including not only the Internet but also your company’s network.
Disconnecting from the network prevents the following situations.
- Via the Internet, attackers can steal more information or download viruses
- Spread infection to other devices and systems via the company network
Remember, to minimize damage, the device should be quarantined as soon as it becomes suspicious.
5-2. Remove with security software
Once all network connections have been cut off and further damage prevented, the next step is to remove the Trojan horse with security software and tools.
Security software can detect and remove most viruses, but in some cases, it may not be possible. In that case, please consider measures such as using Trojan horse removal software, considering initialization, and consulting with a vendor.
Please note that if you install multiple security software from different manufacturers at the same time, there is a high risk that they will conflict and not work well.
5-3. Contacting parties with whom data is exchanged, such as business partners
At the same time as using security software to detect and remove suspected infected devices, we also want to contact business partners who exchanged data with those devices.
If the route of infection and the extent of the impact are clear, contacting us is not necessary, but if it is unclear or if there is even the slightest possibility that the infection has spread to your business partners, be sure to contact us to reduce the risk of damage spreading.
6. Measures to prevent Trojan horse infection
There are three main steps you should take to avoid being infected with a Trojan horse:
| 3 ways to prevent Trojan infection |
|---|
|
1. Don’t open unknown email messages or attachment links 2. Only download apps that you trust 3. Perform security updates |
6-1. Do not open unknown email messages or attachment links
To reduce the risk of being infected with a Trojan, it is important to develop a habit of only opening trusted emails, SMS messages, and attachments.
Trojans are often sent as attachment links in emails or messages. Also, if the sender is unknown, the possibility of a phishing email increases.
When you receive an email or message, you tend to open it, but check the sender and title, and open only those that you need to open. Be especially careful when opening links and attachments, even if they come from familiar addresses.